Leveraging AI? It’s Time to Understand Growing Threats.
As AI becomes a key driver of business innovation, it introduces new vulnerabilities, particularly in the form of shadow AI and cyber threats. Discover how Forcepoint customers interact with AI to better understand its usage and how they are mitigating these risks.
March Briefing
February Briefing
January Briefing
2025 Briefing
The more AI The more AI applications,
the stronger the need for web security policies

Medium-sized businesses
Number of AI applications: 20
Deployed web policies for AI: 5

Large businesses
Number of AI applications: 40
Deployed web policies for AI: 8

Mid-level enterprises
Number of AI applications: 67
Deployed web policies for AI: 12

Large-scale enterprises
Number of AI applications: 93
Deployed web policies for AI: 17
March Briefing
#1: DarkCloud HTML smug attachment-based campaign
Activity Dates: February 17
Targeted Sectors: Consumer end users
Volume: 120+
Targeted Location(s): Ireland
- Attack Chain: Email → HTML→ ZIP → EXE ->DLL
- This is a DLL Sideloading attack
- The email requests the recipient to review an attached purchase order, confirm that all technical specifications can be met without deviations, provide an updated production timeline, and issue the corresponding invoice upon confirmation and having HTML file as attachment.
- When the victim attempts to open the HTML file, it silently downloads a malicious ZIP file in the background and redirects the user to legit adobe[.]com
Sample email:

- The malicious ZIP file contains an EXE and a DLL, where the EXE appears clean but loads the malicious DLL to carry out harmful activity.

IOCs
HTML: D6BB8D9F7EECBD709E3C622282D6E96EF797C5AE
ZIP: 42C36235E35DC3134B089F540444292AAB0A5DB7 -
DLL: F4EDBA4F1B1CB5D53608EE32164355F6EEE67F36
Protection Statement
Forcepoint customers are protected against this threat at the following stages of attack:
- Stage 2 (Lure) - Spam emails are blocked by Cloud rules
- Stage 4 (Dropper File) - The dropper files are added to Forcepoint malicious database and are blocked.
#2: SimpleHelp Remote admin tool URL based campaign
Activity Dates: 20 – 22 March
Targeted Sectors: Consumer end users
Volume: 220+
Targeted Location(s): Israel
- Attack Chain: Email → URL → EXE
- This technique is “living off trusted services” attack where hackers hide malicious files on legitimate platforms like GitHub so the link doesn’t look dangerous at first glance.
- The email is written in Hebrew and urges the recipient to “verify personal details” immediately to avoid delays in receiving a so-called security grant. It includes a call-to-action link directing the user to a personal area for verification. This creates a sense of urgency and leverages financial incentive to manipulate the recipient into clicking the following link:
- hxxps://github[.]com/nitzanigadi-rgb/RR/raw/refs/heads/main/Run-POLICE-0226[.]exe
Sample email:

-
When the recipient clicks the link, it redirects to a malicious site that triggers the download of an executable file, which installs a remote access administration tool on the system.
IOCs
URLs:
Hash:
- hxxps://github[.]com/nitzanigadi-rgb/RR/raw/refs/heads/main/Run-POLICE-0226[.]exe
- SHA1 :61d4b61d6d483ed33995864ecd40ff1e1170834b
Protection Statement
Forcepoint customers are protected against this threat at the following stages of attack:
- URL blocked by Real Time Scanning
- Stage 4 (Dropper File) - The dropper files are added to Forcepoint malicious database and are blocked
February Briefing
#1: Epstein files email bait-and-switch campaign
Activity Dates: February 17
Targeted Sectors: Businesses
Volume: 3
Targeted Location(s): United States
- Spammers are using a sensational and trendy subject line, such as ‘Found your name in Epstein Files’, to lure recipients into opening their emails. The body then includes an apology like ‘Apologies for the unexpected subject line — I just wanted to make sure this caught your attention.’ The rest of the message shifts into sales oriented questions and promotional content.
- Email claims to come from unduitham.com, but is actually sent via Salesforce Marketing Cloud bulk mail infrastructure (*.mta.salesforce.com, *.bnc.salesforce.com).
- Header contains X-SFDC-EmailCategory: apiMassMail X-SFDC-EmailCategory: apiMassMail
- Catchy subject: No legitimate communication would use mass-mail delivery with a personal, urgent, alarmist subject line.
Sample email:
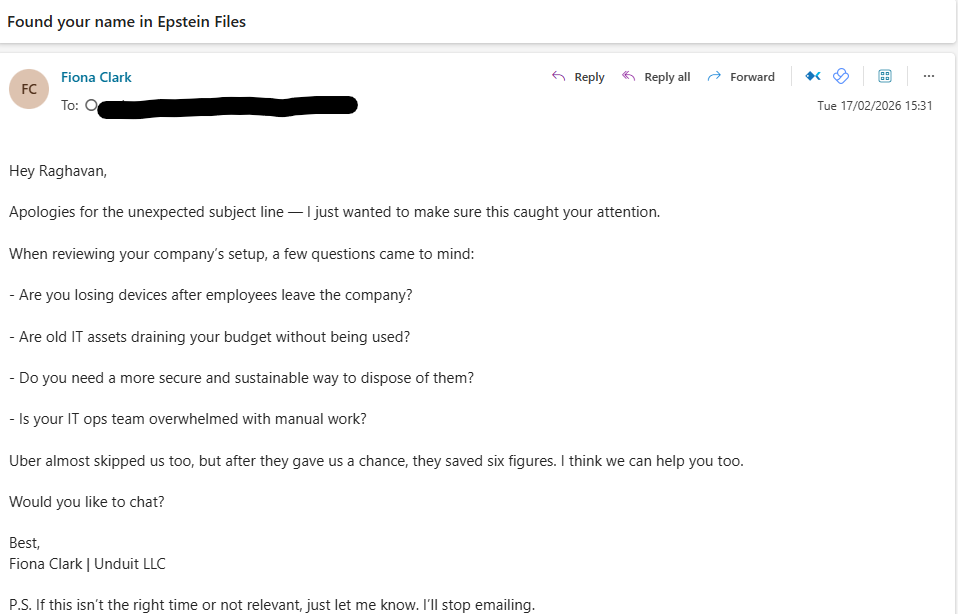
IOCs
- Sender address fiona.clark@unduitham[.]com
Protection Statement
Forcepoint customers are protected against this threat at the following stages of attack:
-
- Stage 2 (Lure) - Spam emails are blocked by Cloud rules
#2: Free web hosting redirect campaign
Activity Dates: February 20
Targeted Sectors: General
Volume: 3
Targeted Location(s): Ukraine
- Campaign uses catchy name, an obfuscated JavaScript loader that reconstructs hidden code at runtime to perform browser redirects or load external resources
- Web pages containing Ukraine name and hosted on Weebly site
- hxxp://fundsukraine[.]weebly[.]com
- hxxp://ukrainenewsletter[.]weebly[.]com
- hxxp://ukrainearts[.]weebly[.]com
- The content of pages appears to be generic, non-Ukraine related blog posts, mainly about gaming, tech topics and other unrelated material.
- But code contains obfuscated JavaScript redirector used on SEO‑spam pages to secretly forward visitors to a malicious second‑stage site.
Ukraine campaign sample page 1:

Ukraine campaign sample page 2:

Ukraine campaign sample page 3:

IOCs
URLs:
- hxxp://fundsukraine[.]weebly[.]com
- hxxp://ukrainenewsletter[.]weebly[.]com
Protection Statement
Forcepoint customers are protected against this threat at the following stages of attack:
- URL blocked by Real Time Scanning (Live RTSS)
January Briefing
#1: Phantom Stealer attachment-based campaign
Activity Dates: 7 January – 26 January 2026
Targeted Sectors: Businesses, Governments and Banks
Volume: 3,000+
Targeted Location(s): United Kingdom, India and Pakistan
- Attack Chain: Email - > HTML-> ZIP - > BAT -> PS1 → Process Injection
- Phantom Stealer attacks were already surging in frequency and sophistication, and were still active as of January 2026.
- Delivered via a malicious HTML attachment disguised as a B2B payment invoices.
- Email has HTML Smug attachment which contains embedded Base64 stream and JavaScript code. Once user opens HTML, it downloads a ZIP file that contains a BAT file. BAT further drops PowerShell and performs process injection targeting .Net processes.
- It scans nearby Wi‑Fi networks and displays detailed information.
- It launches Firefox and Chrome browsers with security and resource‑related restrictions disabled, while forcing it to use a temporary custom profile.
- Uses SMTP to exfiltrate data.
Subject Lines Used:
- Confirm your account
- Re: REVISED Purchase Order
- Payment Confirmation Copy
Sample email:
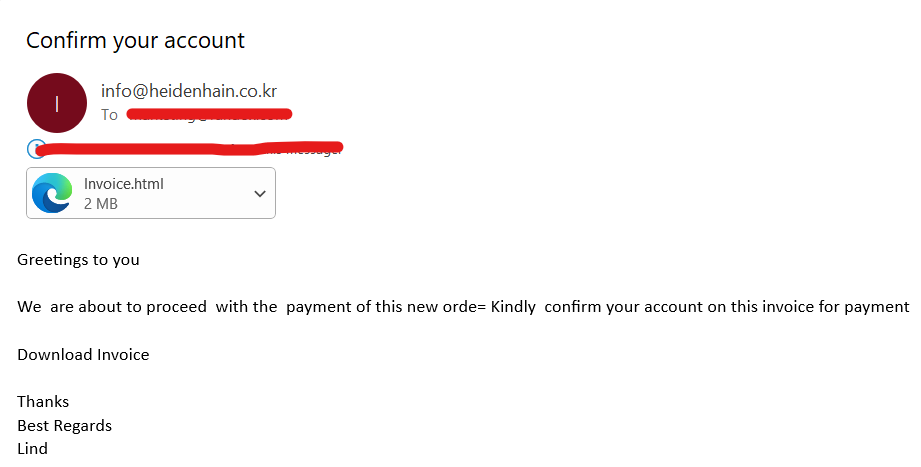
Hashes:
- 2F2E13A9B4B1177705A2F7137382E4B35EA06645 - HTML
- a91b5ddca78598e1e85bf7f1fbc855be879cf726 - BAT
- 4585a1b23eb51277056ec26926ac316788c23b45 - EXE
SMTP C2s:
- mail[.]grupomaspaq[.]com
- mail[.]poskirantekstil[.]com
- eraqron[.]shop
IOCs
Protection Statement
Forcepoint customers are protected against this threat at the following stages of attack:
- Stage 2 (Lure) - Malicious emails are blocked by Cloud rules. Archive attachments are detected by Yara.
- Stage 4 (Dropper File) - The dropper files are added to Forcepoint malicious database and are blocked.
- Stage 5 (Call Home) - Blocked C&C URLs
Why Securing AI Matters for Your Organization
AI brings tremendous value, but its risks cannot be ignored. Hence, organizations leveraging AI must ensure their data, applications, and infrastructure are secure to protect against the rising tide of cyber threats.
Steps You Can Take Today
- Audit your AI usage to understand potential vulnerabilities.
- Implement robust web security policies to mitigate risks.
- Partner with Forcepoint for AI-driven security solutions that protect your business at every stage of an attack.
Want to know more about how Forcepoint secures your AI usage and keeps your organization safe?
